The last 18 months made one thing obvious: autonomous and semi-autonomous "agentic" browsers are going to transact on the web. Whether you call them shopping copilots or fully automated checkout agents, they will browse, compare, and buy. Payments teams must assume an adversarial world—fraudsters will exploit bots, merchants will harden, and regulators will enforce strong customer authentication (SCA). The goal isn’t to outsmart security but to integrate it intelligently so that agents remain reliable, compliant, and measurable.
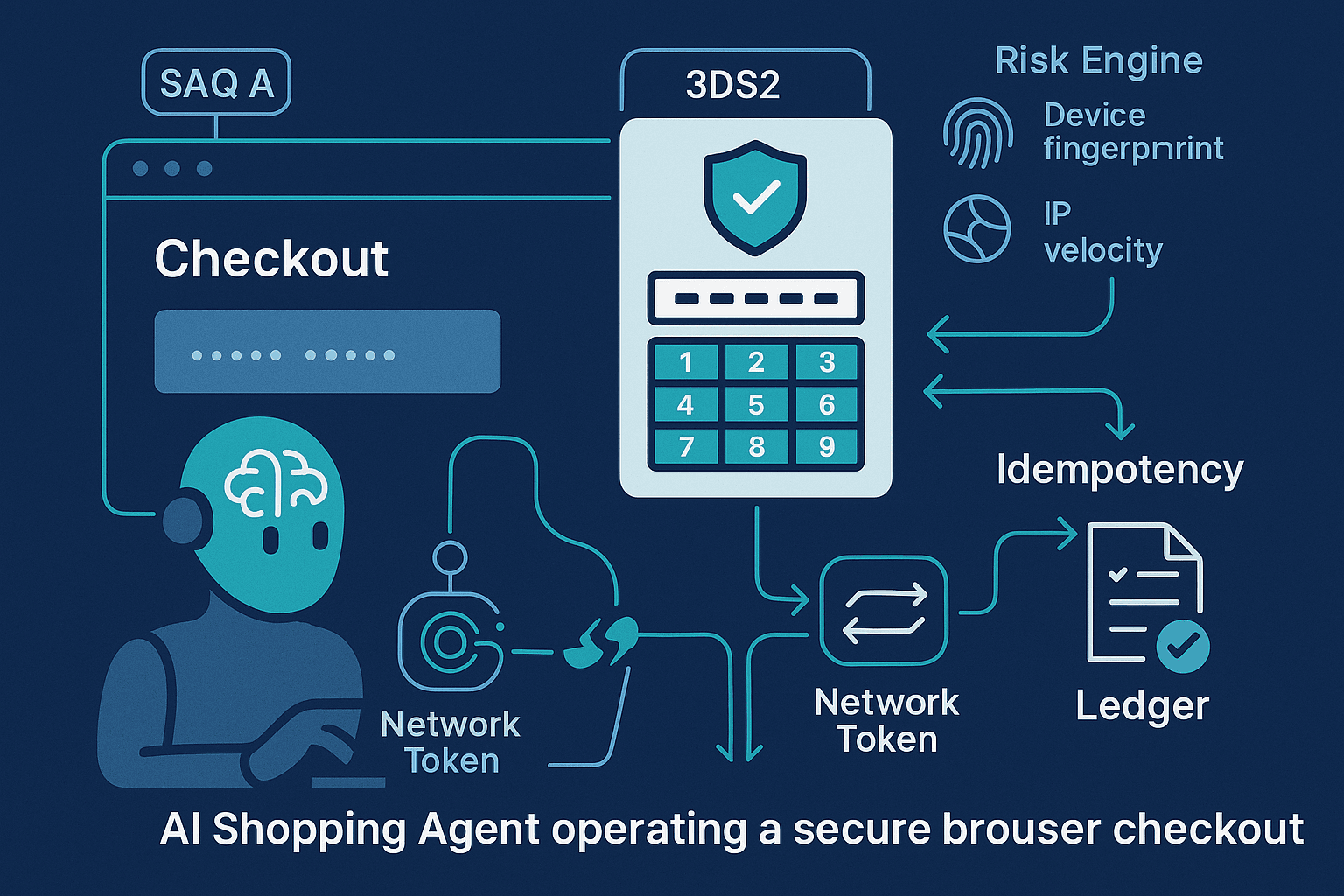
This article lays out a practical, strongly opinionated blueprint for building PCI‑safe browser checkout with AI agents, using network tokens, 3DS2, OTP challenges, idempotent retries, anti‑fraud telemetry, and robust reconciliation. It favors standards, reduces PCI scope to SAQ A whenever possible, and treats the AI agent as an untrusted client by default.
Sections
- Constraints and threat model for AI browser checkout
- Architecture overview: keep PCI scope tiny (SAQ A) and centralize risk
- Vaulting and tokenization: network tokens over raw PANs
- Address normalization: determinism beats cleverness
- SCA/3DS2: frictionless, challenge, and decoupled flows (what to automate vs. not)
- OTP handling: let ACS collect it—don’t build your own OTP forms
- Idempotent retries: keys, lifetimes, and gateway semantics
- Anti‑fraud telemetry: capture, minimize bias, and act in real time
- Order lifecycle and reconciliation: deterministic matching, ledgers, and webhooks
- Code patterns (TypeScript, Python) for idempotency, eventing, and normalization
- Operational checklist and pitfalls
- Constraints and Threat Model Agentic browsers differ from human checkouts in ways that matter to payments:
- Automation and speed: Agents can attempt multiple carts rapidly, triggering rate limits and fraud scores.
- Determinism: Agents should be predictable across retries and merchants; nondeterministic UI flows are brittle.
- Trust boundary: The agent operates in hostile territory (the open web). Treat it as an untrusted client.
- Regulatory obligations: PSD2/SCA in the EEA and UK, plus 3DS mandates by issuers. Agents must play by those rules.
- PCI DSS: Minimize scope. Handling Primary Account Numbers (PANs) directly increases your audit burden and blast radius.
Threats to plan for:
- Replay and duplicate charges due to retries and network hiccups.
- OTP phishing or mishandling if you incorrectly try to capture SCA codes yourself.
- Device/student/farm bot fingerprints that look anomalous or headless.
- Ad‑hoc HTML scraping that breaks when ACS UIs or merchant pages change.
Opinion: Make SAQ A your north star. Avoid collecting raw PANs. Use network tokens and wallets when possible. Defer 3DS to a gateway with a certified 3DS Server. Instrument the living daylights out of your telemetry, and build idempotency into every stateful API call.
- Architecture Overview: Keep PCI Scope Tiny (SAQ A) and Centralize Risk A robust architecture for AI agents looks like this:
- Untrusted agentic browser: navigates merchant UI, but never handles full card PANs directly. For merchants you control, render hosted fields (iframe) from a PCI‑certified PSP, or use wallets.
- Payments broker service (trusted backend): owns customer vault records, network tokens, risk scoring, 3DS flows via PSP APIs, idempotency, retries, and reconciliation. It exposes a narrow client API to the agent.
- Instrumentation pipeline: collects device and session telemetry from the agent (JS signals, HTTP hints, network stats, UI timing) and from the payment provider (3DS frictionless vs challenge, issuer response codes).
- Data segregation: PII and PCI data isolated; token references flow to general services, but PANs never do.
Surfacing into the merchant UI:
- Hosted fields or Elements for card entry (if user is involved). For autonomous agents with pre‑vaulted instruments, use network tokens and skip card UI entirely.
- Apple Pay / Google Pay / Click to Pay to get network tokens and SCA coverage with minimal friction.
- Vaulting and Tokenization: Prefer Network Tokens Tokenization tiers:
- PSP tokens: Gateway‑scoped tokens created by PSPs. Good for portability within that PSP, less portable across PSPs.
- Network tokens (EMVCo): Issuer and scheme‑backed tokens (e.g., Visa Token Service, Mastercard MDES, Amex TSP). They replace the PAN with a device PAN (DPAN) and support lifecycle events (re‑tokenization, cryptograms) and improved authorization rates.
- Wallet tokens: Apple Pay/Google Pay supply network tokens plus dynamic cryptograms. They also often satisfy SCA.
Why network tokens for agents?
- Higher authorization rates and fewer false declines, especially for recurring/COF (card‑on‑file) and credential‑on‑file MITs.
- Lifecycle updates: when a card is reissued, the network token can remain valid via automatic updates, reducing failed payments.
- Stronger binding between token, merchant, and device profile.
Best practices:
- Onboard customers into a vault that prefers network tokens. Your PSP or a dedicated token requestor provides this.
- Maintain Token Requestor ID (TRID), token status (active/suspended), last 4, brand, BIN metadata, and token cryptogram requirements.
- For multi‑PSP strategies, store a broker‑level token record that maps to PSP network tokens per acquirer.
Never have your agent handle raw PANs. If you must collect card data under specific merchant constraints, use iframe‑based hosted fields so the PAN never traverses your servers or the agent’s runtime.
- Address Normalization: Determinism Beats Cleverness Address anomalies fuel AVS mismatches and fraud triggers. Normalize deterministically:
- Use a canonicalization library or API: libpostal, USPS Address Validation (US), Loqate, Melissa, or national postal databases.
- Normalize before vaulting: store both the customer‑entered (or agent‑extracted) address and the canonical form.
- Apply consistent formatting rules per country (UPU S42 guidance):
- Split house number, street, unit/suite.
- Uppercase and remove punctuation where required by the country.
- Use ISO 3166‑1 alpha‑2 for country, ISO 3166‑2 for regions where supported.
- Be conservative about deduplication: use a stable hash of the canonical form, but keep raw variants.
Example: canonicalization with libpostal (Python)
pythonimport json from postal.parser import parse_address from postal.expand import expand_address RAW = "221B Baker St., Flat B, London NW1 6XE, UK" # Parse into components components = parse_address(RAW) parts = {k: v for v, k in components} # Deterministic casing and keys normalized = { "house_number": parts.get("house_number", "").upper(), "road": parts.get("road", "").upper(), "unit": parts.get("unit", "").upper(), "city": parts.get("city", "").upper(), "postcode": parts.get("postcode", "").upper(), "country": "GB" } print(json.dumps(normalized, indent=2))
For a production system, align your AVS strategy with acquirer expectations per region. Some acquirers rely primarily on numeric street and postcode; ensure those can be extracted consistently.
- SCA/3DS2: Frictionless, Challenge, and Decoupled Flows 3DS2 flows to design around:
- Frictionless: Issuer approves based on risk data with no user challenge. Provide rich RBA data to help issuers approve.
- Challenge: Issuer presents a 3DS challenge (OTP, bank app approval, biometric, or knowledge‑based). The ACS (issuer’s Access Control Server) hosts the UI.
- Decoupled authentication (3DS 2.2+): Issuer authenticates the cardholder out‑of‑band (bank app push). Merchant receives auth result later.
Key rule: Do not build your own 3DS UI. Use your PSP’s certified 3DS Server/SDK. The ACS collects the OTP or approval directly. Your page may embed the challenge in an iframe/modal controlled by the PSP/ACS, but you never see the OTP.
For agentic browsers:
- Aim for frictionless first: supply device data, billing/shipping consistency, and order history signals to the 3DS request. Proper telemetry increases frictionless rates.
- Support decoupled flows: If the bank triggers out‑of‑band app approval, your agent must poll the 3DS status or receive a callback and resume the flow.
- Have a human‑approval escape hatch: In autonomous scenarios with expected step‑ups, allow a human-in-the-loop to complete the challenge via QR or app link when required.
Data elements to enrich 3DS requests (examples):
- Account age, last password change, shipping address age, prior transactions count/value.
- Device signals: user agent, timezone, language, screen, WebGL hash, IP ASN, history of successful payments for the user.
- MIT flags and SCA exemptions when applicable (e.g., TRA, low value), via your PSP’s parameters.
- OTP Handling: Let the ACS Handle It Anti‑pattern: Presenting your own input for a bank’s OTP challenge.
Correct pattern:
- Embed or redirect to the ACS challenge hosted by the issuer/PSP. The ACS collects the OTP.
- Do not log keystrokes, clipboard, or JS events in the challenge frame. Treat it as a secure boundary.
- For decoupled challenges, display clear status and allow the customer to switch to another instrument if approval lingers.
For AI agents that operate without the customer present, avoid flows that rely on OTP delivered via SMS/email. Instead:
- Pre‑vault with network tokens and an initial SCA while the user is present.
- Use Merchant Initiated Transactions (MIT) with proper flags and stored credential frameworks after initial SCA.
- Prefer wallets (Apple Pay/Google Pay) where the user’s device provides SCA at vault time.
- Idempotent Retries: Keys, Lifetimes, and Gateway Semantics Agents will retry. Networks will blip. Issuers will time out. Without idempotency you will double‑charge.
Principles:
- Every create‑ish API call (auth, capture, refund) must accept an idempotency key.
- Keys should be: deterministic per semantic operation (e.g., one key per order authorization attempt), collision‑resistant, and have a server‑enforced TTL.
- Server must store the first response and replay it for duplicate keys.
What to bind into the key:
- Operation type (authorize|capture|refund)
- Merchant account and store
- Logical order ID
- Payment method fingerprint (token id, last4+brand if needed)
- Amount and currency
- Cart hash (skus+qty+price) if relevant
Avoid binding ephemeral values that change on retried requests (e.g., new 3DS data or a new cryptogram). Instead, keep the key stable for the intended operation and treat 3DS re‑authentication as a new authorization attempt with a new key.
Client example (TypeScript) for retries:
tsimport crypto from 'crypto'; function idempotencyKey(op: string, orderId: string, amount: number, currency: string, tokenId: string) { const base = `${op}:${orderId}:${amount}:${currency}:${tokenId}`; return crypto.createHash('sha256').update(base).digest('hex'); } async function authorize(order) { const key = idempotencyKey('auth', order.id, order.amount, order.currency, order.tokenId); const res = await fetch('/payments/authorize', { method: 'POST', headers: { 'Content-Type': 'application/json', 'Idempotency-Key': key }, body: JSON.stringify({ orderId: order.id, tokenId: order.tokenId, amount: order.amount, currency: order.currency }) }); return res.json(); }
Server example (Node/Express) enforcing idempotency:
tsimport express from 'express'; import bodyParser from 'body-parser'; import { pspAuthorize } from './psp'; import { getIdem, putIdem } from './idemStore'; const app = express(); app.use(bodyParser.json()); app.post('/payments/authorize', async (req, res) => { const key = req.header('Idempotency-Key'); if (!key) return res.status(400).json({ error: 'Missing Idempotency-Key' }); const cached = await getIdem(key); if (cached) return res.status(200).json(cached); try { const { orderId, tokenId, amount, currency } = req.body; const pspResp = await pspAuthorize({ orderId, tokenId, amount, currency }); await putIdem(key, pspResp, /* ttlSec= */ 24 * 3600); res.json(pspResp); } catch (e) { res.status(502).json({ error: 'upstream_error', detail: String(e) }); } }); app.listen(3000);
Gateway semantics:
- Some PSPs provide idempotency headers (e.g., Idempotency-Key) and dedupe on their side—use them, but keep your own layer as well.
- For capture/refund, use a new key per operation but bind to the same order and authorization reference.
- Expire keys after a safe window (e.g., 24–72h) but persist permanently in your ledger to defend against duplicate provider callbacks.
3DS nuance and retries:
- If an authorization fails due to authentication issues, initiate a new 3DS transaction (new serverTransID) and then a new authorization with a new idempotency key.
- Do not reuse an old CAVV/AAV across different authorization attempts unless explicitly permitted by your PSP/scheme guidance.
- Anti‑Fraud Telemetry: Capture, Normalize, Decide Your agent should look less like a bot farm and more like a stable, consistent customer device.
Collect (ethically, with consent and disclosure):
- Network: IP, ASN, IPv4/6, jitter/RTT statistics, proxy/VPN signals.
- Browser: user agent, platform, timezone, locale, canvas/WebGL hash, font list hash, touch support, storage availability, reduced motion preference.
- Behavior: page dwell time, number of product detail views, add‑to‑cart path, attempted merchants per hour, checkout speed metrics.
- Payment context: instrument age, token type (network vs PSP), shipping/billing congruence, AVS/CVV results, issuer BIN risk info.
Normalize into a stable event schema:
json{ "event": "checkout_attempt", "ts": 1731000000, "session_id": "s_abc123", "user_id": "u_42", "order_id": "o_9001", "device": { "ua": "Mozilla/5.0 ...", "tz": "+0100", "lang": "en-GB", "webgl": "hash_xyz", "ip": "203.0.113.10", "asn": 64500, "vpn_proxy": false }, "payment": { "token_type": "network", "brand": "visa", "bin": "411111", "avs": "Y", "cvv": "M", "sca": { "requested": true, "method": "3ds2", "frictionless": true } }, "cart": { "items": 3, "value": 129.99, "currency": "USD" } }
Real‑time usage:
- Compute a risk score and conditionally request 3DS or push for frictionless.
- Hard block obvious automation abuse (excessive concurrency, IP rotation, impossible geodesic movement) before payment.
- Provide issuers with richer data to improve frictionless approvals.
Bias and privacy:
- Avoid features that proxy for protected classes. Focus on behavior and device consistency.
- Keep IPs and device identifiers scoped and expire them per privacy policies.
- Order Lifecycle and Reconciliation Your system must reconcile asynchronous provider events with your orders deterministically.
Core tenets:
- Every payment attempt is a row with stable identifiers: idempotency key, PSP transaction id, scheme references (e.g., RRN, ACI), and 3DS IDs (serverTransID).
- All provider webhooks are deduplicated by provider event id and sequence number.
- A lightweight ledger records: auths, captures, voids, refunds, chargebacks, and adjustments. Immutable append with compensating entries.
Webhook handler (Python Flask) with dedupe:
pythonfrom flask import Flask, request, jsonify from storage import get_event, put_event, upsert_payment app = Flask(__name__) @app.post('/webhooks/psp') def psp_webhook(): evt = request.get_json() evt_id = evt.get('id') if get_event(evt_id): return jsonify({"status": "duplicate"}) put_event(evt_id, evt) payment_ref = evt["data"].get("payment_ref") status = evt["data"].get("status") upsert_payment(payment_ref, evt["data"]) # idempotent upsert return jsonify({"status": "ok"}) if __name__ == '__main__': app.run(port=4000)
Reconciliation loop:
- Daily: pull PSP settlements/payouts, match by transaction reference and amount, resolve FX fees.
- Roll up per order: ensure sum(captures) - sum(refunds) equals net recognized revenue.
- Mark stale authorizations for reversal if unused within your hold window.
Chargeback handling:
- Store scheme case id and reason code.
- Link to the original idempotency key and order.
- Automate evidence collection (address match, delivery proof, 3DS authentication data) and respond within SLA.
- Practical Code Patterns A) Selecting the right instrument: prefer network tokens first
tstype Instrument = { id: string; type: 'network_token' | 'psp_token' | 'wallet'; brand: string; last4: string }; function chooseInstrument(instruments: Instrument[]): Instrument | null { const byPriority = (t: Instrument['type']) => instruments.filter(i => i.type === t); return byPriority('wallet')[0] || byPriority('network_token')[0] || byPriority('psp_token')[0] || null; }
B) Initiating 3DS2 via PSP (pseudocode)
ts// Pseudocode: your PSP SDK will differ async function initiate3DS(psp, order, instrument) { const threeDSData = await psp.create3DS2Authentication({ amount: order.amount, currency: order.currency, token: instrument.id, billingAddress: order.billingAddress, shippingAddress: order.shippingAddress, customer: order.customer, deviceData: order.deviceData, // pass rich telemetry challengeWindowSize: '02' // e.g., 390x400; choose sane defaults }); if (threeDSData.frictionless) { return { status: 'authenticated', cavv: threeDSData.cavv, eci: threeDSData.eci }; } // Render challenge via provided iframe/URL await psp.renderChallenge(threeDSData.challenge); const result = await psp.poll3DSResult(threeDSData.transactionId); return result.success ? { status: 'authenticated', cavv: result.cavv, eci: result.eci } : { status: 'failed' }; }
C) Authorization with idempotency
tsasync function authorizeWith3DS(psp, order, instrument) { const threeDS = await initiate3DS(psp, order, instrument); if (threeDS.status !== 'authenticated' && order.requiresSCA) { throw new Error('SCA failed'); } const key = idempotencyKey('auth', order.id, order.amount, order.currency, instrument.id); return await psp.authorize({ idempotencyKey: key, token: instrument.id, amount: order.amount, currency: order.currency, threeDS: threeDS.status === 'authenticated' ? { cavv: threeDS.cavv, eci: threeDS.eci } : undefined }); }
D) Address canonical hashing for dedupe
pythonimport hashlib def address_fingerprint(addr: dict) -> str: ordered = [ addr.get('house_number','').upper(), addr.get('road','').upper(), addr.get('unit','').upper(), addr.get('city','').upper(), addr.get('region','').upper(), addr.get('postcode','').upper(), addr.get('country','').upper(), ] return hashlib.sha256('|'.join(ordered).encode('utf-8')).hexdigest()
E) Hosted fields (do this, not raw PAN)
html<!-- Your page loads PSP JS to mount PCI-hosted iframes for card number, expiry, CVC. --> <div id="card-number"></div> <div id="card-expiry"></div> <div id="card-cvc"></div> <script src="https://psp.example.com/sdk.js"></script> <script> const psp = new PSP({ merchantId: 'mid_123' }); psp.mount('#card-number', { field: 'number' }); psp.mount('#card-expiry', { field: 'expiry' }); psp.mount('#card-cvc', { field: 'cvc' }); async function tokenize() { const result = await psp.tokenize(); // result.token is a PSP or network token; send token to backend await fetch('/vault/add', { method: 'POST', body: JSON.stringify({ token: result.token })}); } </script>
- Strategy: Minimize Challenges and Maximize Reliability
- Use wallets and network tokens to reduce the need for step‑ups. Wallet cryptograms and device SCA usually satisfy issuer risk models.
- Send the richest possible RBA data for 3DS frictionless decisions.
- Cache and reuse device data within privacy limits to present a stable profile over time.
- Implement exponential backoff with jitter on network retries but always with idempotency.
- When an issuer indicates soft decline for SCA, restart with 3DS immediately.
- For AI‑led purchases on third‑party sites, prefer flows that accept wallets (Click to Pay) or guest checkouts that redirect to ACS without brittle DOM scraping. If the site blocks automation, fall back to human‑in‑loop approval or pre‑negotiated API integrations.
- Compliance Posture
- PCI DSS: Aim for SAQ A by using hosted fields or wallets. If you ever touch PANs, your scope balloons.
- PSD2/SCA: Use 3DS2 and relevant exemptions. For MIT after initial SCA, apply stored credential framework markers with your PSP.
- Data retention: Minimize PII, set deletion schedules, and mask logs. Never log PANs or OTPs.
- Vendor management: Keep AOC/AOQ for PSPs and token providers, track TRID and scheme contracts.
- Observability and SLAs
- Correlate everything: request_id, order_id, idempotency_key, psp_txn_id, serverTransID.
- Dashboards: frictionless rate, challenge success rate, auth rate by BIN/issuer, soft vs hard declines, retry savings due to idempotency, webhook latency.
- SLOs: 99.9% authorize API availability, <250 ms p95 broker latency excluding PSP time, <2 min p95 webhook reconciliation.
- Testing and Chaos
- Simulate issuer timeouts and soft declines (code 65, 3DS required) and verify your retry + 3DS loop.
- Fuzz addresses and ensure canonicalization stability.
- Rotate device fingerprints to ensure your risk model flags anomalies but avoids false positives for legitimate customer device changes.
- Load test ACS challenge rendering to ensure UI and agent state handling don’t deadlock.
- Operational Checklist
- Tokenization
- Prefer network tokens or wallets; maintain TRID and token status.
- Never store PANs; ensure SAQ A scope.
- Address
- Canonicalize and hash; store raw + normalized.
- Validate AVS expectations per region.
- 3DS/SCA
- Use PSP 3DS server; do not capture OTPs directly.
- Support frictionless, challenge, and decoupled.
- Idempotency
- Mandatory key on all write operations.
- Persist responses; replay on duplicates; set TTL.
- Telemetry
- Device, network, behavioral; normalize schema; privacy‑aware.
- Real‑time risk scoring to influence SCA.
- Reconciliation
- Immutable ledger; webhook dedupe; daily payouts match.
- Chargeback pipeline with evidence collection.
- Reliability
- Backoff + jitter; circuit breakers for PSP outages; fallback instruments.
- Security
- CSP headers to isolate hosted fields/ACS iframes; frame‑ancestors policy aligned to PSP docs.
- No keylogging or event listeners inside challenge frames.
- Common Pitfalls
- Building your own 3DS challenge UI or asking the user to "enter your bank OTP here"—don’t. The ACS collects OTPs.
- Retrying authorization without idempotency, leading to duplicates.
- Treating network tokens as a black box without tracking lifecycle events, causing silent failures when tokens are suspended.
- Overfitting anti‑fraud on user agent strings or single features; use ensembles of stable signals.
- Failing to link all transaction artifacts (order id, idempotency key, PSP id, serverTransID), making reconciliation painful.
- Example End‑to‑End Flow for an AI Agent
- User pre‑vaults a card via hosted fields; network token issued and stored with TRID metadata; initial SCA completed.
- Agent constructs an order: items, shipping, normalized addresses, device profile.
- Broker evaluates risk; sets SCA preference to frictionless, but is ready for challenge.
- Broker initiates 3DS2 through PSP with full RBA data. Frictionless succeeds.
- Broker authorizes with idempotency key A. Issuer approves.
- Merchant ships; broker captures with idempotency key B.
- Webhook arrives confirming capture; ledger appends capture event and marks order paid.
- If network hiccup: client resends with same keys; server replays cached response. No double charges.
Where the agent fits: It never touches PANs, it does not solve OTPs, and it follows redirects/iframes for ACS when necessary. If challenge/decoupled is needed and the user is not present, the broker defers and notifies the user for approval or switches to a previously authorized MIT flow where compliant.
Closing Thoughts Agentic checkout won’t excuse you from compliance or card scheme rules. The path to reliability is to embrace them: use network tokens and wallets, enrich 3DS with good data, treat the agent as untrusted, and make every payment call idempotent. The payoff is measurable—higher auth rates, fewer duplicates, cleaner reconciliation—and it’s the only sustainable way to scale AI‑driven commerce in the real world.
Further Reading
- EMVCo 3‑D Secure 2.3.1 specification (overview and data elements)
- Visa Token Service, Mastercard MDES, American Express Token Service documentation
- UPU S42 address formatting standards
- PCI DSS SAQ A guidance from the PCI Security Standards Council
- PSD2 RTS on Strong Customer Authentication and Common and Secure Communication